Electrical and Computer Engineering ETDs
Publication Date
Summer 7-15-2020
Abstract
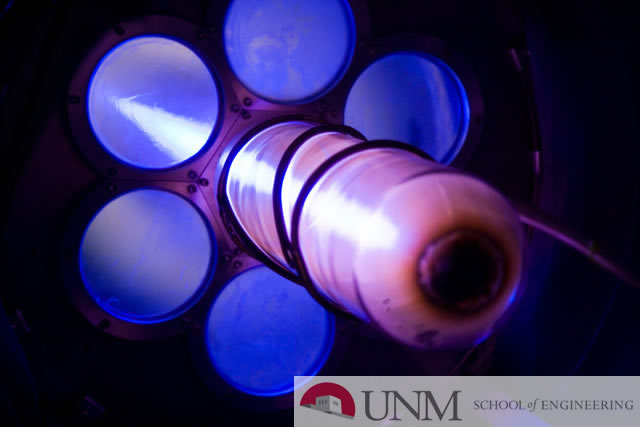
Software routines that deviate from the original algorithm’s goal due to a perturba- tion agent is a phenomenon that has been observed for a long time now. From unin- tended executions on flight control computers during the dawn of space exploration, passing through hardware Trojans tampering in corporate security, to sensitive med- ical equipment compromised to the point of changing the amount of delivered drug, the time intervals, and the reported biomedical measured data, such intrusions are a major risk challenging society. In this dissertation, a computer under perturbation is modeled by a hybrid sys- tem that captures the digital nature on the discrete part, and the interaction of the perturbation signal with the hardware on the continuous part, like extreme electro- magnetic interference (EEMI) on logic circuits. From this point, the dissertation develops in three directions. First, we develop a testbed simulation environment of a 4-bit processor with the ability to take perturbation signals both in time and space. Second, we formulate of mathematical models of the computer logic that take perturbation signals as inputs. And third, we use reachability theory to access how far the perturbation propagates through hardware to cause an exploitable deviation in software execution. We formulate two modifications to the traditional Hamilton- Jacobi-Evans equations (HJE). A diffusion term is added to the original HJE and we also include the second-order terms of the Taylor expansion of the optimality principle.
Keywords
Reachability Software Execution Computing Systems
Sponsors
AFOSR Grant FA9550-15-1-0171
Document Type
Dissertation
Language
English
Degree Name
Electrical Engineering
Level of Degree
Doctoral
Department Name
Electrical and Computer Engineering
First Committee Member (Chair)
Edl Schamiloglu
Second Committee Member
Gregory Heileman
Third Committee Member
Chaouki Abdallah
Third Advisor
Sameer Hemmady
Recommended Citation
Valbuena Reyes, Luis Ariel. "Software Execution under Extreme Electromagnetic Interference." (2020). https://digitalrepository.unm.edu/ece_etds/553


