Electrical and Computer Engineering ETDs
Publication Date
Fall 12-1-2016
Abstract
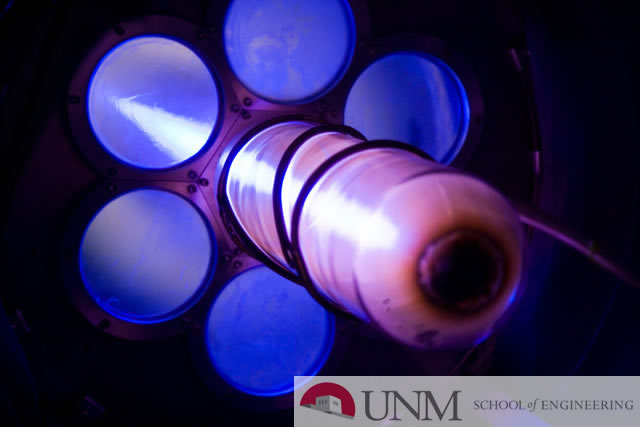
In the context of hardware systems, authentication refers to the process of confirming the identity and authenticity of chip, board and system components such as RFID tags, smart cards and remote sensors. The ability of physical unclonable functions (PUF) to provide bitstrings unique to each component can be leveraged as an authentication mechanism to detect tamper, impersonation and substitution of such components. However, authentication requires a strong PUF, i.e., one capable of producing a large, unique set of bits per device, and, unlike secret key generation for encryption, has additional challenges that relate to machine learning attacks, protocol attacks and constraints on device resources. We describe the requirements for PUF-based authentication, and present a PUF primitive and protocol designed for authentication in resource constrained devices. Our experimental results are derived from a 28 nm Xilinx FPGA.
In the authentication scenario, strong PUFs are required since the adversary could collect a subset of challenges and response pairsto build a model and predict the responses for unseen challenges. Therefore, strong PUFs need to provide exponentially large challenge space and be resilient to model building attacks. We investigate the security properties of a Hardware-embedded Delay PUF called HELP which leverages within-die variations in path delays within a hardware-implemented macro (functional unit) as the entropy source. Several features of the HELP processing engine significantly improve its resistance to model-building attacks. We also investigate a novel technique that significantly improves the statistically quality of the generated bitstring for HELP.
Stability across environmental variations such as temperature and voltage, is critically important for Physically Unclonable Functions (PUFs). Nearly all existing PUF systems to date need a mechanism to deal with “bit flips” when exact regeneration of the bitstring is required, e.g., for cryptographic applications. Error correction (ECC) and error avoidance schemes have been proposed but both of these require helper data to be stored for the regeneration process. Unfortunately, helper data adds time and area overhead to the PUF system and provides opportunities for adversaries to reverse engineer the secret bitstring. We propose a non-volatile memory-based (NVM) PUF that is able to avoid bit flips without requiring any type of helper data. We describe the technique in the context of emerging nano-devices, in particular, resistive random access memory (Memristor) cells, but the methodology is applicable to any type of NVM including Flash.
Keywords
Physical Unclonable Function, PUF-Based Authentication, Delay Model, Security Analysis, Entropy Analysis, Reliability
Document Type
Dissertation
Language
English
Degree Name
Computer Engineering
Level of Degree
Doctoral
Department Name
Electrical and Computer Engineering
First Committee Member (Chair)
Jim Plusquellic
Second Committee Member
Manel Martinez-Ramon
Third Committee Member
Fareena Saqib
Fourth Committee Member
Jim Aarestad
Recommended Citation
Che, Wenjie. "Model Building and Security Analysis of PUF-Based Authentication." (2016). https://digitalrepository.unm.edu/ece_etds/307


